
Radiant Logic & Zscaler target M&A access bottlenecks
about 1 hour agoAcquirers could cut months from post-deal IT integration, as the tie-up aims to let staff use applications on day one after closing.

Asian stories
Singapore software security gap exposed in JFrog study
Despite strong governance on paper, Singapore firms are struggling to enforce software security controls as AI and open-source use accelerates.
Digital Realty expands Malaysia footprint with Cyberjaya hub
Malaysia gains a new global operator as Digital Realty begins building capacity for cloud and AI demand in Cyberjaya.
Asia boards rank cyber attacks as top liability risk
Cyber resilience now sits at the centre of Asian boardroom risk planning, with 76% of directors citing data loss and attacks as key concerns.
MWC Shanghai adds AgiBot, Siemens & Vodafone speakers
Visitors will see AI, robotics and Formula E showcases as MWC Shanghai broadens beyond telecoms to industrial tech and startups.
Visionbay chooses Netris for Taiwan's largest GPU cluster
Hardware-enforced tenant separation will help Visionbay scale Taiwan's largest GPU cluster without risking customer data leakage or network outages.
Corsearch joins Philippines eCommerce pact on fakes
The pact aims to curb counterfeit sales across major marketplaces by using shared intelligence and AI checks before listings go live.
Expert Opinions
More opinions →

What Swiss Cheese teaches us about choosing MDR
MDR buyers risk missing attacks if they focus on price and log limits instead of coverage across identities, endpoints and cloud systems.
about 12 hours ago

While OT security is maturing, risk is not slowing down
Longer dwell times and rising ransomware threats are exposing gaps in industrial defences, despite better OT visibility and governance.
about 13 hours ago

KYC for Neobanks in Asia region
Fast-growing digital banks in Asia face tighter checks as varied rules and weak data systems make customer verification harder across borders.
1 day ago

Stop confusing demos with POCs - Your pipeline depends on it
4 days ago

Navigating Asia's Digital Infrastructure: The Strategic Role of ...
6 days ago

Microsoft security landscape shifts as critical vulnerabilities ...
7 days ago

Your Immune System Doesn't Wait. Neither Should Your Security
14 days ago
Latest News
More news →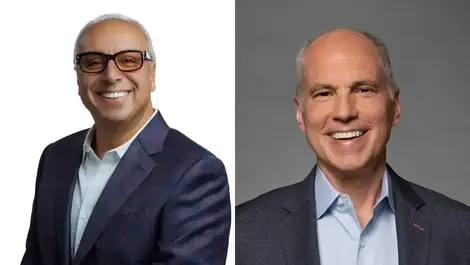
ConnectWise launches AI-native platform for Predictive IT
MSPs could trim ticket loads and lift margins as the new platform ties AI automation to service workflows and security operations.

PureVPN launches ChatGPT tool for VPN server access
Users in 10 markets can now find and connect to PureVPN servers through ChatGPT prompts, without sharing data with the chatbot.

Fime wins MOSIP accreditation for biometric testing
The certification could help governments avoid faulty enrolment hardware that risks undermining digital ID schemes used by more than 100 million people.

Insurers face cyber & climate loss surge, NTT DATA says
Uninsured cyber and climate claims are widening a gap that could leave insurers exposed to more than USD $700 billion in losses by 2030.
Our Editorial Team
Every story is shaped by real people: journalists, editors and contributors.
Mark Tarre
News Chief
Mark Tarre is the News Chief at TechDay, where he leads newsroom operations across the global network and oversees the accuracy, quality, and relevance of technology news coverage. A journalist and PR writer with nearly a decade of experience, he has worked across newsrooms, public relations, and digital publishing. He holds a degree in journalism.

Owen McCarthy
Reviewer
Owen McCarthy has had a long love affair with all things technical since the dawn of the computer age. A child of the 1960’s, he agrees with legendary author, Douglas Adams, that digital watches were a pretty neat idea. By the 1980’s Owen was learning how to code using C and by the turn of the century, he was teaching HTML to enthusiastic youngsters. These days, Owen can be found pestering editors for new technology to review on an annoyingly regular basis. In his spare time, he rides motorcycles of the three-wheeled variety, studies theology, aqua-jogs, and works hard to honour his late wife’s request to live a joy-filled life.

Sean Mitchell
Publisher
Having started his career at Renaissance. Sean joined Apple in Melbourne for a number of years before working in the media space. This started with Review Publishing and later the tech publisher IDG Communications. In 2006 he was involved in the launch of The Channel magazine. As they say – the rest is history.

Sofiah Nichole Salivio
News Editor
Sofiah Nichole has balanced a dual passion for technical precision and the written word since 2017. Before diving into the world of Civil Engineering, she spent years navigating school press conferences and contributing to university publications, honing her skills as a versatile staff writer. Outside of her engineering labs, you can find her advocating for student voices and looking for the next great story to tell. She believes that whether you are building a bridge or a news report, the foundation must be rock solid.

Tom Richmond
Reviewer
Originally from the Isle of Man, Tom has been contributing for Techday for a number of years. He loves sport, tech and cars. In his spare time, you’ll either find him on the golf course, playing football or test-driving a new car.

Anthony Caruana
Interview Editor
Anthony has been living and breathing technology since he was a child. He has contributed to almost every major technology publication in Australia as well as editing a few along the way. In his spare time, he likes to run, especially on trails, and plays Australian Rules football through the winter.
Analyst Insights
Industry research and analysis from leading firms.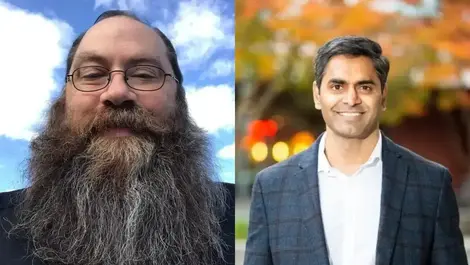
Averlon launches Precog to block exploitable risks
Security teams are under pressure as attacks can now begin before patches land, making early risk detection critical.
Yesterday

Tanium named Forrester leader in endpoint management
Large enterprises under pressure to speed up patching and visibility now have a stronger shortlist option after Forrester ranked Tanium a leader.
3 days ago

Phishing costs rise to USD $51,948 per analyst yearly
Attackers are using generative AI to flood inboxes, pushing phishing to 36.5% of security teams' hours and USD $51,948 per analyst yearly.
3 days ago
.webp)
New Relic launches AI coding observability feature
It aims to close monitoring gaps as firms adopt multiple AI coding assistants, with spending, productivity and compliance now harder to track.
4 days ago