Trend Micro has elaborated on US-CERT reporting that there is memory corruption bug that, when used by unauthorised parties, could cause a Denial of Service (DoS) on various Windows operating systems – and there's no solution available yet.
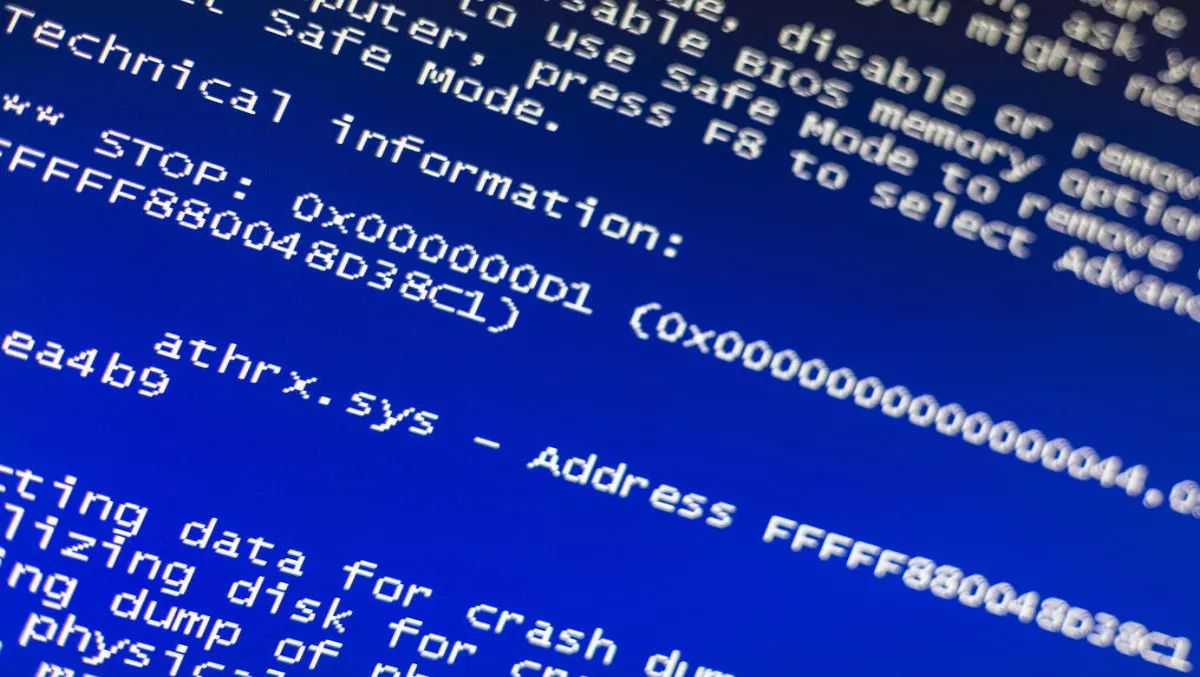
The bug DoS can then crash the operating systems, rendering the DoS attack. The zero-day bug was found in Server Message Block (SMB) traffic that affects Windows 10, Windows 8.1, Server 2016 and Server 2012, Trend Micro says.
The SMB protocol is a network file sharing mechanism used to provide shared access to files, printers, serial ports and other network connections.
A Twitter user posted a Proof of Concept code to show how the bug could lead to a DoS attack and how the bug also leaves an operating system open to remote arbitrary code execution.
“Upon discovery, the bug was initially graded with a severity level of 10 out of 10, which means that the vulnerability could easily be exploited even by untrained perpetrators. Not long after, this rating was lowered to a 7.8,” Trend Micro states.
Although attackers would have to use social engineering to prompt users to connect to a malicious SMB server. This is easily done, as victims only need to click on a malicious link and then connect to a remote SMB server. This would result in a crash, and the blue screen of Death Trend Micro continues.
While US-CERT says there's no current solution for the vulnerability, sysadmins should block outbound SMB connections from local networks to WAN. Microsoft has said it will be issuing a patch for this vulnerability in the Patch Tuesday updates, scheduled for February 14.
Trend Micro Deep Security shields networks through the Deep Packet Inspection (DPI) rule: 1008138-Microsoft Windows Stack Overflow Remote Code Execution Vulnerability.
