Singapore MINDEF opens doors to white hat hackers
The Singapore Ministry of Defence (MINDEF) cyber chief David Koh is asking budding security experts to hack MINDEF systems – all with the aim of improving defences against the malicious hackers.
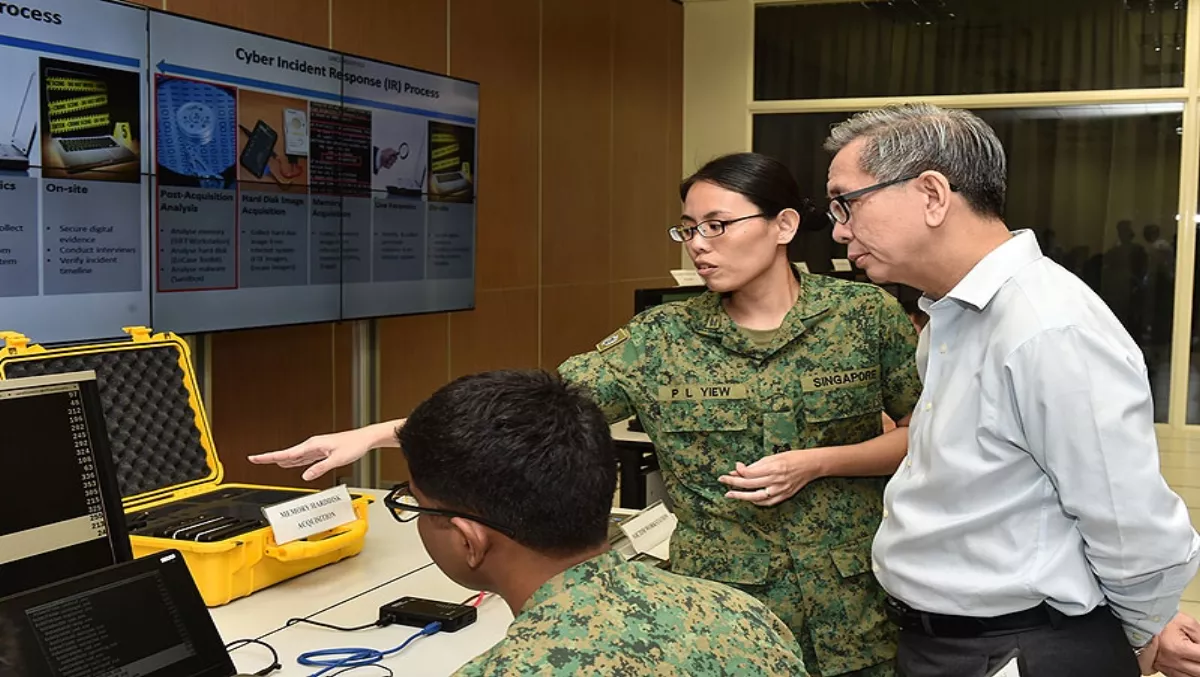
Koh, who is also chief of the Cyber Security Agency of Singapore (CSA), announced the MINDEF Bug Bounty Programme this week. The announcement comes off the back of his visit to the Cyber Defence Test and Evaluation Centre (CyTEC) on Tuesday.
The MINDEF Bug Bounty Programme is the first initiative for any Singapore Government agency.
Bug bounty firm HackerOne will run the programme between January 15 and February 4 2018.
The programme will bring a select number of white hat hackers from around the globe who will test major MINDEF internet-facing systems for vulnerabilities and receive rewards for doing so.
The rewards could range from S$150 up to S$20,000 dependent on the number and quality of vulnerabilities discovered.
"The total amount paid out in rewards is dependent on the number and quality of the vulnerabilities discovered, and is expected to cost significantly less than hiring a dedicated commercial cybersecurity vulnerability assessment team," MINDEF says.
The eight MINDEF systems are as follows:
- MINDEF Website (Ministry of Defence website)
- NS Portal (e-Services for NSFs and NSmen)
- CMPB Website (Central Manpower Base website)
- DSTA Website (Defence Science and Technology Agency website)
- eHealth (Portal for MINDEF/SAF personnel for medical purposes)
- Defence Mail (MINDEF/SAF Internet email service and I-Net)
- LearNet 2 Portal (Learning resource portal for trainees)
- myOASIS Portal (NSmen administration portal)
Koh says the crowdsourcing method is an innovative way of emphasising the importance of Singapore's cyber defences and the need for improvement.
"This is the first time that MINDEF is launching such a bold programme. White hat hackers participating in this programme will be given the mandate to 'hack' MINDEF, to find bugs in our major Internet-facing systems… For each valid and unique bug that the hacker finds, he will receive a bounty," he says.
According to MINDEF, the agency is an attractive target for malicious cybersecurity. Koh adds that it is not possible to fully secure modern computer systems, particularly as new vulnerabilities are discovered every day.
The crowdsourcing approach is both effective and fast, just as the cyber landscape is changing fast, Koh says.
HackerOne has conducted similar bug bounty programmes in the past for the United States Department of Defense, Intel and Twitter.


