Locky ransomware variant mimics Konica Minolta copier emails
A Locky ransomware variant is doing the rounds again and this time it is disguising itself as not only common vendors, but also office equipment from Konica Minolta.
Researchers from Comodo's Threat Intelligence Lab spotted the campaign in September, which is able to hide from machine learning and algorithm-based tools.
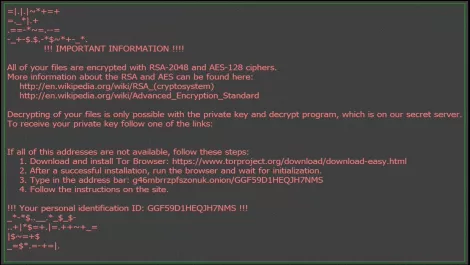
It uses social engineering to infect machines with Locky ransomware, encrypt data and ask for a ransom of between 0.5 to one Bitcoin (US$4000).
The attacks are also part of a larger botnet of computers located mostly in Vietnam, Mexico, India and Indonesia.
Southeast Asia, India, Europe and the Americas were heavily impacted by the attacks, as well as locations such as Australia, New Zealand and Indonesia.
Many of the attacks take the form of a genuine-looking email that closely mimics that of the Konica Minolta C224e copier, popular in offices around the world.
"Employees today scan original documents at the company scanner/printer and email them to themselves and others as a standard practice, so this malware-laden email looks quite innocent but is anything but harmless," researchers state.
The email subject line features the subject line 'Message from KM_C224e' and contains a malicious attachment.
Other emails take the form of common fake invoice statements, the the subject line 'Status of invoice'.
In both phishing emails, the encrypted files take a .ykcol extension and .vbs files are distributed via email. This is different to previous Locky attacks, which used different extensions.
"These types of attacks utilize both botnets of servers and individuals' PCs and new phishing techniques using social engineering for unsuspecting office workers and managers. This enables a very small team of hackers to infiltrate thousands of organizations and beat A.I. and machine learning-dependent endpoint protection tools, even those leading in Gartner's recent Magic Quadrant," comments Fatih Orhan, head of Comodo Threat Research Labs.
Researchers suspect the new variations are designed to not only for social engineering, but also to fool security administrators and machine learning tools.
Researchers say ISPs were heavily coopted during the attacks. Vietnam Posts and Telecommunications sent 18,824 emails as part of the 'Message from KM_C224e' attack.
The attack also drew on 19,886 different IP addresses from 139 different country code top-level domains.
The 'Status of invoice' attack drew on 12,367 different IP addresses from 142 country code domains.
"Because the new ransomware appears as an unknown file, it takes a 100% 'default deny' security posture to block or contain it at the endpoint or network boundary; it also requires human eyes and analysis to ultimately determine what it is - in this case, new ransomware," Orhan concludes.
