The Ultimate Guide to Encryption
A curated Asian edition of TechDay news, analysis, interviews, reviews, job moves, and related resources for Encryption.
What to know about Encryption
Encryption plays a crucial role in protecting digital information from unauthorized access, ensuring privacy and data security in an increasingly connected world. This tag gathers diverse stories on encryption technologies, strategies, and challenges faced by enterprises and individuals alike.
Recent discussions highlight the rising adoption of quantum-safe encryption, cloud-based key management solutions, and zero trust architectures, reflecting the evolving cybersecurity landscape. Companies such as DigiCert, Entrust, Gemalto, and others are actively advancing encryption offerings to prepare for emerging threats like quantum computing and sophisticated malware leveraging encrypted channels.
Readers exploring this tag can learn about innovations in encryption software and hardware, the importance of encryption in data protection regulations, and the complexities of managing encrypted traffic to prevent security blind spots. The collection also emphasizes the critical balance between privacy, regulatory compliance, and safeguarding against malicious actors who exploit encryption.
Whether you are a cybersecurity professional, IT decision-maker, or simply interested in data protection, following these stories will deepen your understanding of encryption’s essential role in securing information today and in the future.
Asian Encryption News
Regional stories with direct local relevance
Ransomware drives 58% of Singapore cyber incidents
More than 130 major incidents in 2025 show Singapore facing rising disruption, with public services and retailers hit hardest.

Women behind quantum: Resilient systems start from within
In quantum security, a young engineer shows how women's resilience and collaboration are vital to building safer post-quantum systems.

BW Digital and Squareroot8 plan quantum-secure link
BW Digital and Squareroot8 plan quantum-secure link between Singapore and Batam, targeting post-quantum protection for data and AI workloads.

Google Cloud opens Bangkok region in USD $1 billion push
Google Cloud opens its first Bangkok region in a USD $1 billion Thailand push, promising AI growth, data residency and thousands of jobs.

HPE boosts retail resilience with new edge & core tech
HPE rolls out new Aruba switches, Marvis-powered analytics and Nonstop servers to keep retail transactions and in-store networks always on.

Squareroot8 & VIAVI forge Asia-Pacific quantum pact
Squareroot8 and VIAVI sign Asia-Pacific pact to embed quantum-safe security into critical telecom and government networks at the fibre layer.
Analyst Insights
Research and market analysis connected to Encryption
IoT Analytics flags seven telecom trends at MWC 2026

Foxit launches document management system in PDF tools

Protegrity launches AI Team Edition for secure inferencing

Survey finds organisations struggle to secure unstructured data

DigiCert posts record Q4 ARR after expansion spree
Expert Columns

Proof beats promise: The trust crisis AI is creating

The why and what of FIPS 140-3 validation in modern cybersecurity

Why AI-powered security needs network telemetry across the hybrid cloud

Atlassian scales AI search with OpenSearch on Kubernetes

Hexnode CEO on how fintech breaches multiply where device visibility ends

Women behind quantum: Resilient systems start from within

Generative AI fuels alarming surge in intimate image abuse

2026 begins: Crypto's heavyweight rumble - round by round

Securing the future: Simplified management, Scalable growth, and built-in compliance for K-12

Enterprises urged to act now on post-quantum security
Interviews
Interviews and video coverage from the networkRecent Encryption News

World App adds encrypted chat & human ID in Malaysia
World rolls out an updated World App in Malaysia, merging encrypted chat with proof-of-humanness checks to tackle bots and deepfakes online.

Drukair chooses Worldpay to boost global payments
Bhutan's Drukair has picked Worldpay as its new global payment gateway to cut cross-border declines and streamline online bookings.

Forward Edge-AI delivers quantum device, wins fifth security patent
Forward Edge-AI delivers Isidore Quantum device to Taiwan's National Central University, securing critical infrastructure with its fifth US patent in quantum-safe communications.
Exclusive: Synology's Thachawan Chinchanakarn on 2025 risks
Nearly 90% of Southeast Asian firms invest in digital transformation, yet many face cyber risks and data management challenges amid budget and expertise gaps.

Beyond AI: The quantum era has begun
Quantum technology is emerging from labs to real-world use, with global efforts, including Singapore's S$300m investment, marking a new computing era beyond AI.

ST Engineering launches quantum-ready security for Singapore banks
ST Engineering launches quantum-safe security solutions to help Singapore banks prepare for future cyber threats from quantum computing advancements.
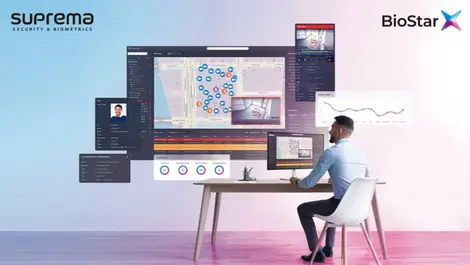
Suprema unveils BioStar X for unified AI biometrics & security
Suprema launches BioStar X, an AI-powered platform unifying biometric access and video surveillance for seamless, scalable security management.
Google & CSA join forces to boost Singapore cyber resilience
Google and Singapore's Cyber Security Agency renew partnership to enhance national cybersecurity with AI tools and public-private training initiatives.

HLF Digital app sees SGD $1 billion in transactions since launch
Hong Leong Finance's HLF Digital app has topped SGD $1 billion in transactions since August, boosting fixed deposits and customer engagement.

Future-proof your business with a cyber resilience strategy
Over 9,000 organisations were hit by a SharePoint breach in July 2025, highlighting the need for cyber resilience beyond basic prevention.
PT KAI partners with Zimbra for secure & sovereign email upgrade
PT Kereta Api Indonesia upgrades its email system with Zimbra's secure, on-premise platform to boost cybersecurity and comply with Indonesian data sovereignty laws.

Suprema renews ISO certifications to boost data protection
Suprema has renewed its ISO/IEC 27001:2022 and 27701 certifications, reinforcing its commitment to data security amid evolving digital threats.

Futurex partners with Cake to launch cloud payment system
Futurex has teamed up with Cake, Vietnam's leading digital bank, to launch the country's first fully cloud-based Card Management System.

Google Cloud & Gulf Edge join forces for Thai cloud service
Google Cloud and Gulf Edge join forces to deliver Thailand's first sovereign cloud, aligning with local data security laws, boosting regional digital innovation.

Ransomware threats escalating in Southeast Asia – report
Escalation in targeted ransomware threats impacts businesses across Southeast Asia, with over 287,000 incidents detected in 2023 alone.

New IBM & NCS partnership to fortify Singapore's data
IBM and NCS partnership to offer quantum-safe, privacy-enhancing services to Singapore's public agencies and enterprises.

SpeQtral & SPTel to construct Singapore's first quantum-safe network
SpeQtral and SPTel to forge Singapore's first nationwide quantum-safe network, bolstering security using quantum cryptography.

Synology creates a data warehouse for Taiwan AI Labs
Taiwan AI Labs has opted for Synology's comprehensive line of storage systems to build the core of its AI training infrastructure.

Akar Inti Teknologi ensures Indonesian FSIs advance cryptographic capabilities
Akar Inti Teknologi and Unbound Security have partnered to provide secure data solutions and services throughout Indonesia. 🌏💻 #Cybersecurity #DataProtection.

Ciena encryption boosts data center security for biggest Korean financial co
KB Kookmin Bank, the biggest financial institution in Korea, has boosted its security with the help of Ciena encryption capabilities.

