
Why network visibility must be the foundation of Zero Trust architecture
In May 2021, U.S. Presidential Executive Order 14028 on improving the nation's cybersecurity was issued, directing federal agencies to transition to a Zero Trust Architecture (ZTA) as they modernise and move to cloud services.
The National Institute of Standards and Technology (NIST) provided guidance on transitioning to a ZTA in Special Publication 800-207 Zero Trust Architecture (SP 800-207).2 In addition, the Office of Management and Budget has released guidance prioritising Zero Trust initiatives.
Although the executive order is specifically for federal agencies, the principles it outlines apply equally well to enterprises and government.
One of the most strategic investments any organisation can make to facilitate a successful ZTA implementation is complete, accurate and timely network visibility into all data in motion across the organisation, including data center, cloud and multi-cloud environments.
Visibility into data in motion is an aspect of Zero Trust that falls within the Activity Logs logical component depicted below: Core Zero Trust Logical Components from SP 800-207.
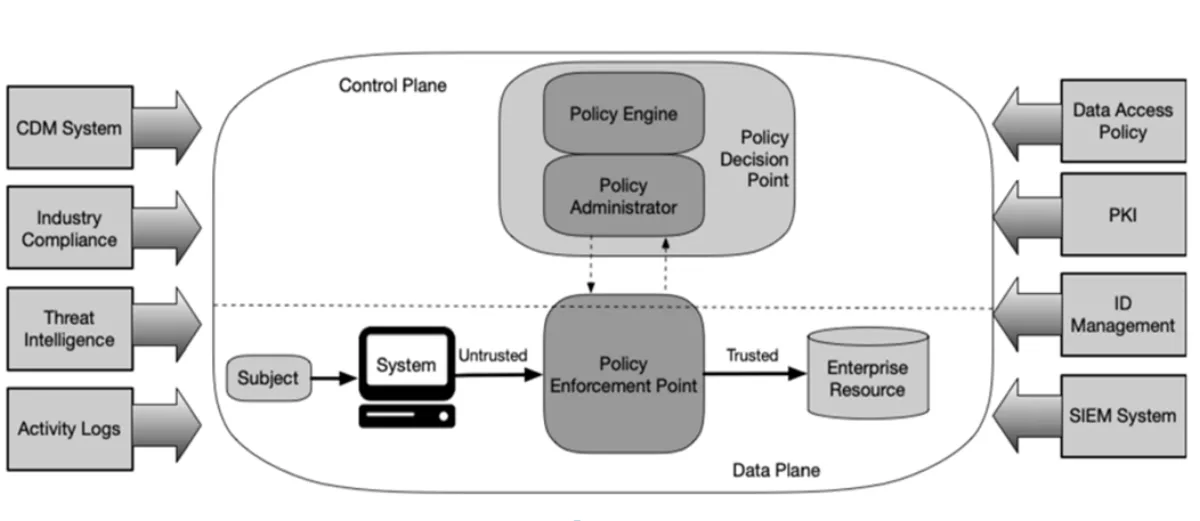
SP 800-207 defines this essential 'network and system activity logs' component as follows: "This enterprise system aggregates asset logs, network traffic, resource access actions and other events that provide real-time (or near-real-time) feedback on the security posture of enterprise information systems.
Many government organisations have also made investments in other areas that can bring value to ZTA approaches, including identity and access management (IAM), endpoint detection and response (EDR), and security information and event management (SIEM) technologies.
However, as organisations evolve towards more mature ZTA implementations, security gaps will remain after the deployment of these technologies. For example, specific nodes such as internet of things (IoT) devices may be incompatible with EDR software, and sophisticated adversaries can manipulate logs from hosts.
A scalable, centralised approach to network visibility mitigates these risks. Moreover, deploying an advanced network visibility platform can further optimise the effectiveness and scalability of ZTA implementations by filtering out noise and duplicate data from the traffic analysed by security tools.
The following are two key reasons why pervasive visibility into all data in motion across the enterprise — including all east-west traffic — is central to ZTA and mitigates risks not otherwise addressed by IAM, EDR, and SIEM implementations. Note that east-west traffic refers to data flows between nodes within a data center and/or cloud service provider (CSP) perimeter.
Monitoring east-west traffic helps organisations detect and respond to attempts by adversaries to move laterally from the initial point of breach towards higher-value assets.
Reason #1 – Data about the network plays a central role in ZTA, and visibility into data in motion is a critical aspect of understanding the current state of the network.
Understanding the state of the network is a key tenet of ZTA as described in NIST SP 800-207: "Tenet 7: The enterprise collects as much information as possible about the current state of assets, network infrastructure and communications and uses it to improve its security posture.
#An enterprise should collect data about asset security posture, network traffic and access requests, process that data, and use any insight gained to improve policy creation and enforcement. This data can also be used to provide context for access requests from subjects.
One of the primary ways organisations can gain this understanding is by collecting and analysing data about network traffic, including access requests. For example, when an advanced network visibility platform is used to address the activity logs component in Figure 2 of SP 800-207, it provides substantial insights about network activity to the policy engine at leading-edge network speeds to inform access decisions.
In addition, analysis of data about network traffic complements can be used to validate the integrity of other types of data that feed the policy engine while satisfying current and emerging federal government security requirements beyond ZTA.8
Reason #2 – Network visibility mitigates risks that cannot be addressed by EDR while also validating EDR telemetry.
Host-based security products such as EDR play a valuable role in ZTA. However, it is crucial to understand that EDR cannot be deployed on all endpoints. This leaves security gaps that require additional measures to mitigate.
Specialised devices such as IoT nodes may not be capable of running EDR agents. Similarly, operational technology (OT) and industrial control system (ICS) environments often contain hosts running proprietary or legacy operating systems that cannot run EDR agents or receive ongoing security patches.
Unauthorised 'shadow IT' nodes and instances of 'malware IT', such as rogue virtual machines and microservices spawned by malware, will also operate without EDR when present. Hence monitoring network traffic for security threats is essential.
Risks may also persist even in cases where EDR software can be installed on hosts. While EDR products are designed to resist tampering, sophisticated threat actors have demonstrated their ability to exploit vulnerabilities in the operating systems that host EDR software, as well as firmware and hardware at levels below the operating system.
In its summary of the SolarWinds incident, threat intelligence and advisory firm Mandiant, Inc. found that once attackers compromised specific nodes, they took steps to circumvent or delete host-based logging mechanisms:
"Mandiant identified the threat actor disabling SysInternals Sysmon and Splunk Forwarders on victim machines that they accessed via Microsoft Remote Desktop in addition to clearing Windows Event Logs.
Similar techniques were used during an insider attack against technology vendor Ubiquiti, Inc. According to security reporter Brian Krebs, the insider took steps to manipulate logging while also blaming the company for the lapses in leaks to the media:
"Among the claims made in those news stories was that Ubiquiti had neglected to keep access logs that would allow the company to understand the full scope of the intrusion. In reality, the indictment alleges, Sharp had shortened to one day the amount of time Ubiquiti's systems kept certain logs of user activity in AWS.
Complementing host-based security technologies like EDR with optimised network detection and response (NDR) and SIEM capabilities based on network visibility data is the best way to mitigate these risks.
For example, observation of network activity to a host that EDR does not log is a strong indicator of a compromise and possible efforts by adversaries to hide command and control traffic. In addition to serving as an additional point of validation, network visibility data is generated externally to any specific host, making it much more difficult for a threat actor to compromise.
Article by Gigamon ANZ manager, George Tsoukas.