SURVEY: 70% of customers would leave a business after a breach
A recent study from Gemalto proves it's not just data that is lost following a breach – you'll lose most of your customers too.
Consumers are evidently happy to relinquish the responsibility of protecting their data to a business, but are expecting it to be kept secure with no effort on their part. And this mentality is due to be enforced further in the face of imminent data regulations like GDPR.
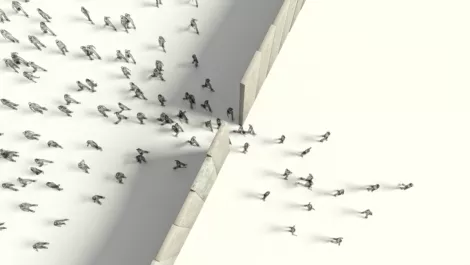
According to Gemalto's survey of 10,000 consumers around the world, 70 percent would stop doing business with a company if it experienced a data breach.
Despite this (and what is no doubt causing headaches in IT security departments worldwide), the survey revealed consumers are failing to properly secure themselves, with 56 percent still using the same password for multiple accounts.
Even in the cases where businesses offer robust security solutions like two-factor authentication, 41 percent of consumers admit ignoring the technology. This may be because the majority believe the business holding their data is ultimately responsible for its security.
This combination is resulting in an alarming amount of breaches – 80 percent – being caused by weak or previously stolen credentials.
Gemalto says quite simply, something must change or this is only going to get worse.